This story has been updated. See below.
Today, I checked on Cleantechnica’s weekly “Pravduh” report, where they list and rank undesirable journalists by their degree of (in Cleantechnica’s view) negative coverage of Californian carmaker Tesla. Be careful when clicking on the link above, because you may (or may not) run into the problem I encountered.
I spent about a minute or so reading Cleantechnica’s complaints that a mainstream media with the “short-term memory of a goldfish” decided on covering Tesla’s firing of 7% of its workforce, instead of reporting more important news, such as “Tesla unveils wall outlet charging station.” I was just about to check Cleantechnica’s leaderboard of (in their view) most repulsive journos (this week, Jim Collins of Forbes is way ahead of Liam Denning of Bloomberg and Nicolas Vega of the New York Post in Cleantechnica-measured disgustingness) when, BAMM, a warning sounded, and a nasty screen interrupted my reading.
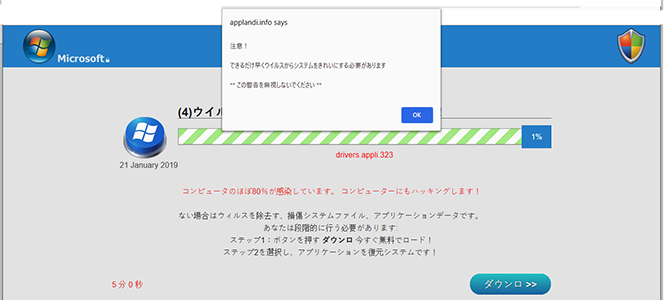
The warning was in Japanese. I live in Japan, and Frau Schmitto-san, summoned to translate, yelled: “It’s one of those fake virus warnings. DON’T click on it.”
Those of us who frequent porn sites, or other dodgy areas of the Internet, may be familiar with those fake virus warnings. Regular folk who prefer to stay in the safe space of cleantech websites would not have made that harrowing experience, so allow me to explain a bit more.
The warning that jumped off the Cleantechnica page was quite convincing. On the left, it was adorned by a Microsoft logo with a little padlock next to it, at the right, it was flanked by a Microsoft Defender logo. A pop-up told me in Japanese that I had contracted a virus, that it is necessary to clean the system ASAP, and I was directed to “not ignore this warning .” At least, they didn’t threaten to cut off a finger – I guess the warning wasn’t that location-aware. (Also, I don’t use Windows Defender, but nice try.)
A handy button promised help for the infected. Would I have clicked on the button, I would have landed on 2cametrack.info, and by now, I would be in a pile of trouble. According to trojan-killer.com, “2cametrack.info is a nasty redirect virus which your PC could obtain after the wrong installation of malware samples.” According to the less excited virus-removal-guide.net, “2cametrack.info redirects can ruin the performance of your browser and make it much slower than before.” Basically, 2cametrack.info seems to hijack your browser, and you would no longer have control over what’s next. The virus it complained about was fake, but you will for sure catch a real virus (or a bunch of them) when hitting the button. You will understand that I didn’t want to find out, and hence I ended my investigation.
The initial malware was transmitted by an ad on the Cleantechnica website. Normally, one would have to click on ads to follow them, but in this case, I was directed to the fake Microsoft virus killer automatically without clicking on any ads or links in the Cleantechnica article. According to the logs, the browser played a quick game of redirect ping-pong between Cleantechnica.com, clubadsme.com, applandi.info, and finally the den of nastiness, 2cametrack.info. Again, all without clicking on anything.
The attacks are not easily reproducible. Other people visiting the site reported no problems. This could have been due to the vagaries of ad distributions, or due to more insidious reasons, such as targeting. We’ll never know.
When I reported the attack, helpful Twitterati suggested that I simply “should get an ad blocker.”
https://twitter.com/wilhitjb/status/1087312459898048512
My answer was that the onus is on Cleantechnica.
It's Cleantechnica's ad network, Cleantechnica's money, and Cleantechnica's responsibility. A website that is so concerned about the moral hygiene of media covering Tesla should spend at least some effort on keeping its own ads disinfected
— BertelSchmitt™ ?????????#fella (@BertelSchmitt) January 21, 2019
In light of recent doxing cases and threats against parties critical to Tesla, caution is in order. In my case, protection against further attacks was easy, but not complete. I simply put clubadsme.com, applandi.info, and 2cametrack.info on my browser blocklist. This doesn’t protect me from attacks via other domains. The only sure-fire solution in this case would be to stay away from Cleantechnica. Until I catch the same, or different, bug from another site, that is.
(P.S.: If you watch the Cleantechnica site for a while, you will see that it refreshes on its own every minute or so, thereby loading a new set of ads while the same set of eyeballs is looking at the page. If you advertise on Cleantechnica, you may want to ask what’s going on.)
Update, 1/23/2019
Cleantechnica chief Zachary Shahan responded today, saying that he has “neither of the problems you describe (malware popup or pages reloading if kept open),” and that his “IT & ad people” are looking into the matter.
@BertelSchmitt Thanks for the note about this: https://t.co/XCPkdEaN51 I have neither of the problems you describe (malware popup or pages reloading if kept open), & have CT pages open all the time. We use common, major ad networks, but am having IT & ad people look into this.
— Zachary Shahan (@zshahan3) January 23, 2019
Cleantechnica’s IT & Ad people seem to still be scratching their heads, because when I accessed the CleanTechnica page in question today, I noticed that it still automatically redirected to clubadsme.com, the jump-off point of the malware described above. Also, on my machine, ads on the CleanTechnica page continued to refresh automatically, without any clicks, approximately once every minute. If Cleantechnica’s ad network serves malicious ads (which it appeared to do) the danger is compounded by new and possibly malevolent ads being uploaded to readers’ computers once a minute and without any user interaction.
Forget about password cracking or breaking into your WiFi. As JavaScript pioneer Douglas Crockford said: “The most reliable, cost effective method to inject evil code is to buy an ad.” There are more than 700 ad networks on the Internet, and a few are bad. The video above explains how to use rogue ad networks for hacking (the good stuff starts at 17:40). In the video, researchers show how they were able to attack tens of thousands of computers at a cost of less than $20. The video is 6 years old, and the problem has gotten worse.
Publishers can mitigate the problem by using only highly reputable ad networks. but even those can sometimes fall prey to a malicious ad. If one is reported, the thing to do is to immediately disconnect the ad network in question, and to have a serious discussion with the ad network.
To be fair, Zachary Shahan’s IT posse doesn’t have an easy job. The ads I see on Cleantechnica are not the ads Zachary sees. Ads can be targeted by region, by interest, with a little work, ads can even be targeted at the individual user. Cleantechnica has been provided with the pertinent links, which should aid them in securing their site. A complete transcript of the repeated redirects can be made available upon request.